BYOD Security Concerns
Many organizations have allowed or encouraged employees to use their own smartphones and tablets on the job. The process is called bring your own device, or BYOD. It’s popular with workers and saves the employer money on equipment costs. However, BYOD has drawbacks that concern security experts.
Last week the Information Security Community on LinkedIn and Internet security firm Vectra Networks released the results of their second annual BYOD & Mobile Security Study. The study involved polling more than 1,100 IT security experts on their top BYOD security concerns.
1. Loss of Company or Client Data
The biggest fear of any IT security professional is losing confidential data. Smartphones and tablets are basically handheld computers and malicious individuals can use them to steal information and cause damage to your corporate systems.
2. Unauthorized Access to Company Data and Systems
With workers bringing their own equipment, the process of administration and granting access is more complex. In addition to workers, the company may also have clients and contractors that need access using their own devices.
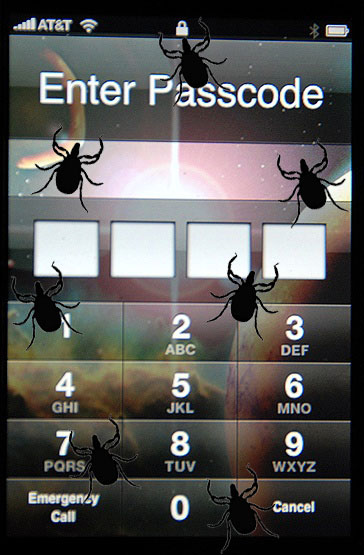
3. Mobile Malware
Viruses, worms and Trojans aren’t limited to computers anymore. The open structure of the Android operating system and the lax screening policy on the Google Play Store makes it a prime target for malware programmers. Antivirus and Internet security developer Symantec has called Android a “malware magnet.”[1] Apple maintains a tighter control on iOS apps, but the iPhone and iPad are not immune from malware either.
4. Installed Apps with Security Flaws or Suspect Permissions
Even if an app isn’t outright malware, it can have built-in security flaws. In April 2014, Fiberlink released the results of a survey of BYOD users that found 83% had 10 to over 100 apps installed on their devices.[2]
It’s highly likely that many of these apps have not been tested for security and compatibility with the employer’s systems. Apps that use advertising to generate revenue often use third-party mobile ad services that add another layer of potential security problems. Many apps have permissions that allow them to share information that may be sensitive with the developer. For example, a game or social media app the user installed on impulse could share the user’s contact list or call history.
Even if your company has not embraced BOYD, it still needs to address the use of personal mobile devices. The BYOD & Mobile Security Study found 21% of organizations that have no BYOD support acknowledge employees are using their own devices for work-related tasks anyway.
[1] http://www.cbronline.com/news/security/symantec-google-android-is-a-malware-magnet-4324588
- Stalking threats still very real for TV actress - 10/16/2024
- CrowdStuck thanks to CrowdStrike - 07/25/2024
- AT&T breach too big to ignore - 07/14/2024


Leave a Reply
You must be logged in to post a comment.