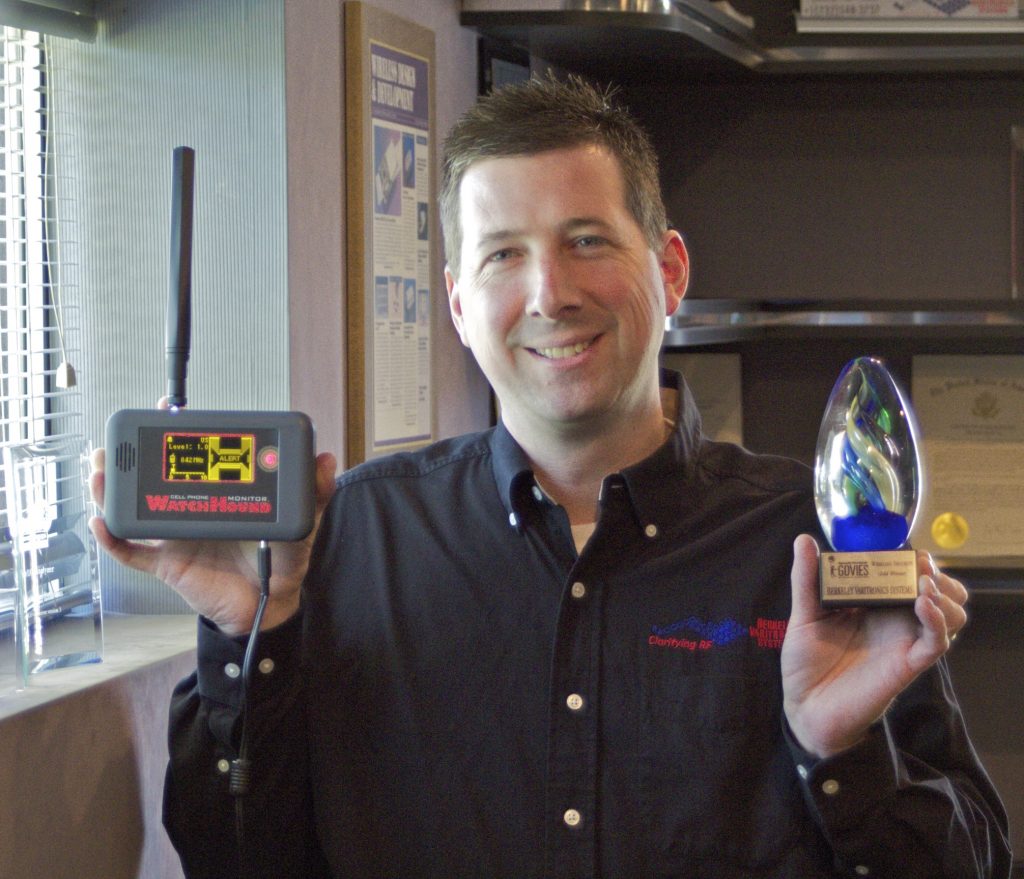
CEO and President
Scott N. Schober is the President and CEO of Berkeley Varitronics Systems (BVS), a 50-year-old New Jersey-based privately held company and leading provider of advanced, world-class wireless test, security, safety and cybersecurity solutions. As an experienced software engineer, Scott invented Berkeley’s cell phone detection tools used to enforce a ‘no cell phone policy’. These instruments are effectively used around the globe to find contraband cell phones smuggled into correctional, corporate, government, military, law enforcement and private facilities.
Recognized Innovator
For outstanding achievement in his field, Scott has been recognized by his peers with the Security Products Magazine New Product of the Year Award, the Security Products Reader’s choice award, the Popular Science 25th Annual Best of What’s New Winner, the ConnectED World Award, the M2M Evolution Product of the Year award as well as many others.
Frequent TV and Radio Subject Expert
Mr. Schober is a highly sought after subject expert on the topic of wireless security and cybersecurity for media appearances and commentary. He has appeared on many ABC/NBC/CBS/FOX affiliate news reports, Bloomberg TV, CBS This Morning, CGTN News, CNBC, CNN, Fox Business, Good Morning America, Inside Edition, MSNBC, Bill O’Reilly No Spin News and many more. His cybersecurity expertise is heard on dozens of radio stations such as NPR, Sirius XM Radio, Bloomberg Radio, The Peggy Smedley Show as well as hundreds of tech/security podcasts. He regularly presents on vital security issues at conferences around the globe discussing wireless technology and its role in the current cybersecurity breaches along with his vision for best practices to stay safe in the future. Scott has been interviewed in WSJ, Forbes, Fortune, Success, NY Daily News, Newsweek, USA Today, The Daily Enquirer and The New York Times.
Sought After Speaker
Scott educates business around the world about how to prepare for a future of Cybersecurity and corporate espionage, opening their eyes to this ever deepening black hole of liability. He also shares his insights into covert cell phone detection and creates awareness to the subtle but powerful influence of drones. He has spoken at RSA, ShowMeCon, GovSec, FutureCon, CyberSecurity Summit, Counter Terror expo, Espionage Research International, Connected World, ConstrucTech, IEEE, GSM World Congress and many more events. Mr. Schober was a VIP attendee at two Concordia Summits both held in New York and was selected to appear in an interview discussing national security.
Contributing Writer and Blogger
In addition to his own weekly blog, Scott is also a regular contributor on the Huffington Post, guest-blogger on TripWire’s State of Security and also writes for HP’s Business Value Exchange.
Top-Selling Author
Scott has authored 3 top-selling cybersecurity books that draw on his decades of experience as business leader, 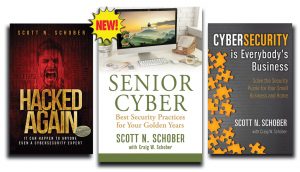 innovator and subject expert. Hacked Again chronicles Scott’s personal experience of being hacked and how he managed to escape from despair and help others to learn from his own mistakes. Cybersecurity is Everybody’s Business details Scott’s experience as a small business owner and provides cautionary insight into hackers’ motives and methods. Senior Cyber addresses the victimization of our senior citizens by hackers and how they can fight back.
innovator and subject expert. Hacked Again chronicles Scott’s personal experience of being hacked and how he managed to escape from despair and help others to learn from his own mistakes. Cybersecurity is Everybody’s Business details Scott’s experience as a small business owner and provides cautionary insight into hackers’ motives and methods. Senior Cyber addresses the victimization of our senior citizens by hackers and how they can fight back.
Educator and Mentor to the Business Community
Mr. Schober is a Cybersecurity Advisory Board Member for Kean University. He is also an Advisory Board Member and regular Cybersecurity Contributing Editor to Connected World Magazine.
Mr. Schober received a Bachelor of Science degree in Computer Science from the University of Kean, NJ in 1992 and thereafter attended graduate studies in telecommunications at New York University, NY.
“I’ve always been fascinated with how things work. That same curiosity that drove my early exploration has made me a relentless scientist, engineer and innovator who sees challenges as opportunities.”
Notable products include Pockethound, a tool that helps educators detect cheating in the classroom, Manta Ray cell phone detector, SentryHound-Pro cell phone detection portal and Wolfhound-Pro used by TSCM professionals worldwide to detect and locate unauthorized cell phones.
Scott Schober is a relentless scientist, engineer, and innovator.
-
- He is determined and follows through with every new project he begins.
- Since he was a child, he always enjoyed taking things apart and creating new things.
- Scott holds numerous patents and has developed more than 50 tools and products that protect and maintain the integrity of information security.
A Few Notable Products:
Pockethound™ is the industry’s most sensitive cell phone detector for it’s size. This award-winning*, passive receiver is no larger or heavier than a deck of cards and specifically tuned to the RF signature of common cell phones including all 2G, 3G and 4G bands.
Manta Ray™ is the answer to the growing problem of unauthorized, illegal, unsecured & contraband cell phone use in correctional facilities, government buildings, corporate environments, financial institutions, universities & law enforcement agencies.
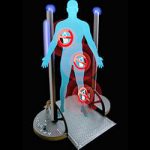
SentryHound™ cell phone detection security portal is triggered when cell phones pass by its sensors. This type of TSCM installation is especially useful for security personnel looking to detect any cell phones as well as some weapons including knives and guns without invasive and time-consuming searches.
Wolfhound™-PRO’s award-winning*, high speed scanning receiver utilizes a multi-band DF antenna system allowing security personnel to locate nearby cell phones in either standby mode* or during active voice, text or data RF transmissions making it the perfect TSCM tool for enforcing your NO WIRELESS security policy.